MetaPhone: The Sensitivity of Telephone Metadata
 Is telephone metadata sensitive? The debate has taken on new urgency since last summer’s NSA revelations; all three branches of the federal government are now considering curbs on access.
Is telephone metadata sensitive? The debate has taken on new urgency since last summer’s NSA revelations; all three branches of the federal government are now considering curbs on access.
Consumer privacy concerns are also salient, as the FCC assesses telecom data sharing practices.
President Obama has emphasized that the NSA is “not looking at content.” “[T]his is just metadata,” Senator Feinstein told reporters. In dismissing the ACLU’s legal challenge, Judge Pauley shrugged off possible sensitive inferences as a “parade of horribles.” On the other side, a number of computer scientists have expressed concern over the privacy risks posed by metadata.
Read more"Kaspersky Lab" prepares antivirus for TV
 Now your TV could be infected by computer viruses. Technology security expert warns cyber criminals could infect millions of devices. Televisions could soon be infected by computer viruses, one of the world's top technology security experts has warned.
Now your TV could be infected by computer viruses. Technology security expert warns cyber criminals could infect millions of devices. Televisions could soon be infected by computer viruses, one of the world's top technology security experts has warned.
Eugene Kaspersky is co-founder and chief executive of Russia’s Kaspersky Lab, the world’s fourth largest computer antivirus company. He said threats will spread to the 'home environment' and televisions as internet connections make technology more vulnerable.Televisions could soon be infected by computer viruses, one of the world's top technology security experts has warned In an interview with The Telegraph he said his company's headquarters in Moscow receives 315,000 suspicious activity reports every day.
Read moreLavaboom builds encrypted webmail service to resist snooping
 A new webmail service called Lavaboom promises to provide easy-to-use email encryption without ever learning its users’ private encryption keys or message contents.
A new webmail service called Lavaboom promises to provide easy-to-use email encryption without ever learning its users’ private encryption keys or message contents.
Lavaboom, based in Germany and founded by Felix Müller-Irion, is named after Lavabit, the now defunct encrypted email provider believed to have been used by former NSA contractor Edward Snowden.
Lavabit decided to shut down its operations in August in response to a U.S. government request for its SSL private key that would have allowed the government to decrypt all user emails.
Read moreTrueCrypt for Windows: No major flaws found in first phase of security audit
 The first round of results are in, and so far TrueCrypt, the popular open-source encryption program, has a relatively clean bill of health. Security firm iSec Partners recently carried out the first phase of the TrueCrypt audit on behalf of the Open Crypto Audit Project (OCAP).
The first round of results are in, and so far TrueCrypt, the popular open-source encryption program, has a relatively clean bill of health. Security firm iSec Partners recently carried out the first phase of the TrueCrypt audit on behalf of the Open Crypto Audit Project (OCAP).
OCAP is the official name for the group behind istruecryptauditedyet.com, a project inspired by the revelations about the National Security Agency’s surveillance activities. OCAP was created by Matthew Green, a cryptographer and research professor at Johns Hopkins University, and Kenneth White, Principal Scientist at Social & Scientific Systems. For its report, which was released on Monday, iSec took a look at TrueCrypt’s latest Windows edition (version 7.1a).
Read moreHere's why it took 2 years for anyone to notice the Heartbleed bug
 What caused the Heartbleed Bug that endangered the privacy of millions of web users this week? On one level, it looks like a simple case of human error. A software developer from Germany contributed code to the popular OpenSSL software that made a basic, but easy-to-overlook mistake.
What caused the Heartbleed Bug that endangered the privacy of millions of web users this week? On one level, it looks like a simple case of human error. A software developer from Germany contributed code to the popular OpenSSL software that made a basic, but easy-to-overlook mistake.
The OpenSSL developer who approved the change didn't notice the issue either, and (if the NSA is telling the truth) neither did anyone else for more than 2 years. It's hard to blame those guys. OpenSSL is an open source project. As the Wall Street Journal describes it, the project is "managed by four core European programmers, only one of whom counts it as his full-time job." The OpenSSL Foundation had a budget of less than $1 million in 2013.
Read moreHow advertising cookies let observers follow you across the web
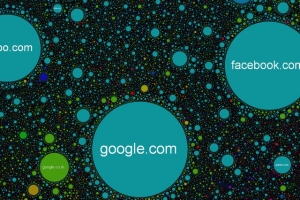 Back in December, documents revealed the NSA had been using Google's ad-tracking cookies to follow browsers across the web, effectively coopting ad networks into surveillance networks.
Back in December, documents revealed the NSA had been using Google's ad-tracking cookies to follow browsers across the web, effectively coopting ad networks into surveillance networks.
A new paper from computer scientists at Princeton breaks down exactly how easy it is, even without the resources and access of the NSA. The researchers were able to reconstuct as much as 90% of a user's web activity just from monitoring traffic to ad-trackers like Google's DoubleClick. Crucially, the researchers didn't need any special access to the ad data. They just sat back and watched public traffic across the network. As it turns out, trackers are displaying a surprising amount of information in public.
Read moreSnowden's revelations prove Internet is no longer safe - survey
 As businessmen tend to choose more secure data protection and storage software in light of Edward Snowden's revelations, researchers are wondering about the potentially dramatic consequences this may have for the future of the Internet.
As businessmen tend to choose more secure data protection and storage software in light of Edward Snowden's revelations, researchers are wondering about the potentially dramatic consequences this may have for the future of the Internet.
A survey of more than 1,000 businessmen across the world shows that most of them favor more secure forms of data storage as the whistleblower's disclosures continue to reverberate. Governments are responding to the trend by encouraging efforts to reroute regional online traffic locally, rather than through the United States. Paradoxically, US high-tech giants, including Facebook and Google, may be hit hard in the coming years by a global backlash against technology "made in the USA".
Read moreGoogle now encrypts Gmail traffic to and from its servers
 Google today filled one more privacy and security hole in its Gmail email service by encrypting all message traffic between email users, the search engine giant's email servers, and its data centers.
Google today filled one more privacy and security hole in its Gmail email service by encrypting all message traffic between email users, the search engine giant's email servers, and its data centers.
The full HTTPS encryption move was the next logical step to protecting Gmail users from the snooping eyes of government or malicious actors. "Starting today, Gmail will always use an encrypted HTTPS connection when you check or send email. Gmail has supported HTTPS since the day it launched, and in 2010 we made HTTPS the default. Today's change means that no one can listen in on your messages as they go back and forth between you and Gmail's servers--no matter if you're using public WiFi or logging in from your computer, phone or tablet," said Nicolas Lidzborski, Gmail Security Engineering Lead, in a blog post announcing the move.
Read moreHow the NSA plans to infect ‘Millions’ of computers with Malware
 Top-secret documents reveal that the National Security Agency is dramatically expanding its ability to covertly hack into computers on a mass scale by using automated systems that reduce the level of human oversight in the process.
Top-secret documents reveal that the National Security Agency is dramatically expanding its ability to covertly hack into computers on a mass scale by using automated systems that reduce the level of human oversight in the process.
The classified files – provided previously by NSA whistleblower Edward Snowden – contain new details about groundbreaking surveillance technology the agency has developed to infect potentially millions of computers worldwide with malware “implants.” The clandestine initiative enables the NSA to break into targeted computers and to siphon out data from foreign Internet and phone networks. The covert infrastructure that supports the hacking efforts operates from the agency’s headquarters in Fort Meade, Maryland, and from eavesdropping bases in the United Kingdom and Japan.
Read moreHow to protect your iCloud Keychain from the NSA
 Apple has released a massive update to its “iOS Security” white paper for IT professionals. It contains more information on iOS security than Apple has ever shared publicly before, including extensive details on Touch ID, Data Protection, network security, application security, and nearly all security-related features, options, and protective controls.
Apple has released a massive update to its “iOS Security” white paper for IT professionals. It contains more information on iOS security than Apple has ever shared publicly before, including extensive details on Touch ID, Data Protection, network security, application security, and nearly all security-related features, options, and protective controls.
For the first time, we have extensive details on iCloud security. For security professionals like myself, this is like waking up and finding a pot of gold sitting on my keyboard. Along with some of the most impressive security I’ve ever seen, Apple has provided a way to make it impossible for agencies like the NSA to obtain your iCloud Keychain passwords.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















